We all love the convenience of mobile technology.
A smart phone with it’s integrated GPS, email, calendaring, office suites, a zillion apps and the ability to call and text is a true wonder of the modern age.
There is also a potential dark side to this technological marvel.
Every time you slip it in your pocket you are on the radar and your movements, position, orientation and conversations are all open to someone. You are carrying the tracking device in your pocket!

Cellphone: The tracking device in your pocket
In the 1960’s, the powers-that-be decided that they needed to intercept, record and catalog every phone call. This project was called Echelon. One thought to be a crackpot, conspiracy theory, has been revealed numerous times, by involved governments, in the 1990’s.
Now, 100% of your communications are captured, and stored for data-mining and to determine if you are a threat. This includes all types of Radio communication on all frequencies!
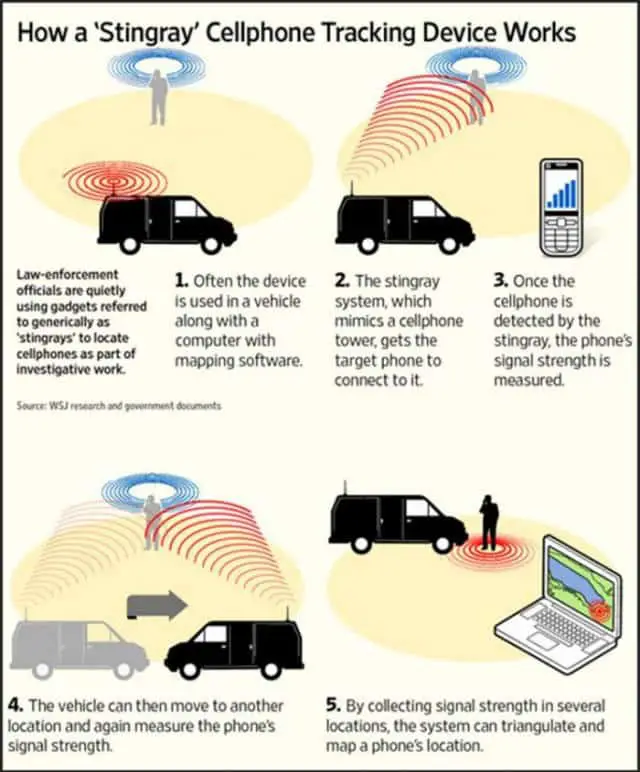
Local, State, and Federal agencies also have Stingray technology. A stingray is a false cell phone tower that can force phones in an area to connect to it. Once these devices connect, the stingray can be used to hone in on the target’s location or to eavesdrop on conversations, text messages, and web browser activity.
This is a “legal” man-in-the-middle attack, where your mobile device has its data routed through a fake cell tower and collected….without warrants.
Shhh… Someone is Listening!
Calls:
Be aware that every call you make, whether it’s on a cell phone, flip phone, land line or VOIP phone is recorded by the government. So no, flip phones are not the answer. Legislative change is the only answer.
You can thank the Echelon program and the Patriot Act (ironic name). This isn’t whacky conspiracy theory stuff, this is the truth. Do some online searches to verify, we always encourage you to fact check everything, with reliable internet data or other research.
If you are on a call, it’s being recorded someplace and run against audio analysis for detecting certain key words and phrases. It will be archived FOREVER, so they can always run the call through the analysis again, when new key words and phrases are added.
These are the keywords that some government agencies use to monitor social media so I’m assuming the key words for Audio Analysis are very similar.
The point to keep in mind here is that you have no privacy in your phone, cell phone, voip and audio/voice communications.
Microphone:
Now that you understand your lack of privacy while using your phone to make calls let’s take it a step further. Your phone’s microphone can be remotely activated even when you are not using the phone.
WHAT?
Yes that is correct. The government (or your cell phone carrier/provider) can remotely turn your cell phone into a listening device (you’re being bugged) EVEN WHEN YOU ARE NOT MAKING A CALL!
Proof: FBI taps cell phone mic as eavesdropping tool
Here is someone’s work around to prevent that (flip phones only): Cell phone privacy modification. Ok, so maybe flip phones are the answer, to respond the the question of this posts title. They seem to be one of the only widely available technology define that can still be modified for better privacy assurances. I say better, because if they want to spy on you (as in, you are targeted), they will find a way.
Location
GPS:
Mobile phone GPS is awesome. It makes it so simple to find places and navigate. What I don’t like is that the government (or carrier/provider) can track my location anyplace, as long as it’s on.
I know what you’re thinking “I’ll just disable, turn off the GPS feature.”!
Good thinking, but WRONG.
Your GPS can be remotely activate and track you, all the while, making your phone lie, and indicate that the GPS is off or disabled. That’s right, the phone will tell you that it’s GPS is off while reporting your location.
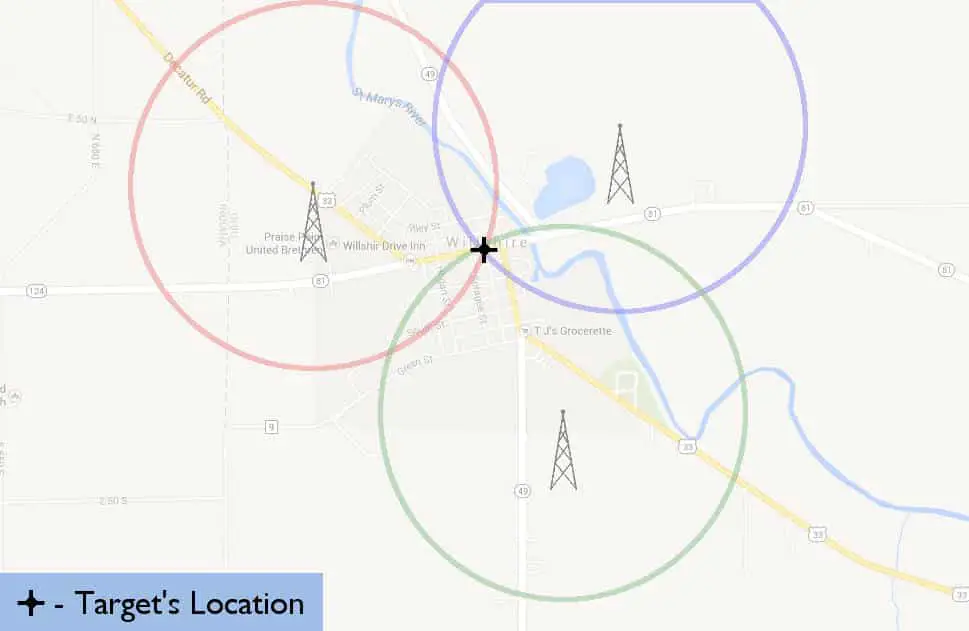
Cell Tower Triangulation:
Even if you don’t have a smart phone, or you figured out a way to block the GPS from remote activation, your location (within 1000 meters) can be triangulated, using your cell phone signal and the towers you are connected to.
Yes, even the cheapest cellphone with no advanced GPS or Smartphone features can be located very easily this way. This data has been used in criminal trials and is pretty well published if you want to read up on it.
What can you do?
Microphone eavesdropping
To avoid remote microphone activation and bugging, take out the battery when you want to have private face to face conversations!
You can also boot the phone into DFU mode (Device Firmware Update), which shouldn’t have have any drivers loaded, except for the USB input and internal storage access. 3G, 4G and GPS, should be unactivated… but this might change in the future.
Avoid Stingray, warrant-less wiretapping and cell phone intercepts
Android users, you can use AIMSICD (Android IMSI-Catcher Detector) to get notified when your cell signal is tampered with.
The AIMSICD app does not:
- Provide secure phone calls (see RedPhone available in the Google Play Store)
- Provide secure SMS (see TextSecure or SMSSecure)
- Provide secure data transmission for your Android Phone (see Orweb browser, which requires Orbot that connects to the Tor mesh)
- Provide app permission control (XPrivacy, requires ROOT access on your phone)
- Provide secure application sand-boxing
- Provide ROOT and remove bloatware
- Provide firewalls (see AFWall+, requires ROOT access on your phone)
- Provide full device encryption
- Prevent already installed rogue applications from full access and spying
Caution: Using this App will not guarantee that you will be shielded against surveillance of any form!
GPS and Location Tracking
Want to a big wake up call? Google knows where you’ve been, almost everywhere you’ve been. See your location history (use your browser that’s logged into a google account – gmail, etc).
Take the battery out of your phone, boot the phone into DFU mode or leave the cell phone at home when you want your location to be private and use a stand alone GPS, good old fashioned road maps or a Road Atlas to get where you’re going.
Don’t put that battery back in until you are someplace that you are fine with being known by others, who might be tracking you. Use your head if you are going to a secret place, leave that battery out until you get back to home or a usual place. This will prevent giving anyone, who’s monitoring you, a heading or direction of travel to your secret place!
A Road Atlas in your car can be worth it’s weight in gold!
General Anonymity
You might want to consider paying cash for a pre-paid phone activating it from someplace neutral (not your home or office) and keeping the battery out of it until you have to use it. Then only use it in public or neutral locations. Remember when you buy more minutes PAY CASH also. You don’t want this “burner” phone tied to you in any way!
A pre-paid phone can only be used for a short while, before your calling trends will start to identify who you are, so you may have to repeat the process of buying a phone and remotely activating it often. This is the price you pay to have a cell phone and maintain your privacy. I agree, it shouldn’t be this way.
We all love our smart phone, even if its the tracking device in your pocket. If the SHTF and I need to bug out and be off the radar, I am removing the battery from this phone, stomping on it and tossing it in a trash can. No GPS on this burner!
Other Ways You Are Tracked
In today’s world of modern technology, you have to take extreme measures to hide and to remain anonymous. The Nazi’s and Secret police would have loved to have had this type of technological tracking to keep it citizens in line. Here in the USA, we even pay the bills for our collars (cell phone, internet access), which they use against us.
What does it take to hide? First you need to know how you are tracked, then you might be able to do something about it.
Internet
There is no privacy on the internet. Encryption may give you some cover, but the best defense now is to use Tails (which uses Tor) from a public or open wifi access point, from a laptop that has never been connected to your network. Add to this some MAC address spoofing and you may just obfuscate and bounce around enough to be anonymous. Unless you still have your cell phone on you. Then they know you were in the proximity of that wireless network, and all bets are off.
More information:
- Internet Communication OpSec
- Surveillance Countermeasures
Cell phone
Good luck going anywhere or having any private conversations on your cell phone. It’s impossible. Your cell phone is tracked and triangulated via the cell phone towers and then top it off with your even more accurate built in GPS.
Add to this that every cell phone call is intercepted, regardless of what the news media tells you.
More information – Cell Phone: The Tracking Device in Your Pocket
Radio
Radio, so far seems to be the most anonymous. Except that on the Amateur bands you must use your amateur radio callsign.
The bad news is, they can still find you, using a method lovingly labeled “Fox Hunting”.
Fox hunting is the method used to track rogue transmitters. It utilizes directional antenna. A directional antenna is more sensitive to received signals in some directions than others. When a directional antenna is rotated, a received signal will either increase or decrease in signal strength, information from which a skilled hunter can determine the likely direction to the transmitter.
If they start hunting you, you have a very limited amount of time to stop transmitting and get the heck out of there.
I speculate that the powers that be have antennas deployed just for this type of tracking, so transmit and move.
You might have the best luck using HF and bouncing that signal, or skipping it off the atmosphere, but nothing is foolproof.
This is just a few ways describing how you are tracked, remember this and you might be able to avoid some of it.